As access control systems become outdated, their performance can deteriorate badly, offering less protection for your building and the people in it.
Whether you’re a facilities or security manager it’s your job to make sure your site is secure. As technology improves, potential security threats get more complex. Your system needs to be kept up to date in order to deal with these threats. However, as with most building systems, it’s only natural to be reluctant to upgrade, due to the effort and costs involved.
We’re The Chris Lewis Group, a Fire and Security system installer based in the South of England. For over three decades, we’ve created state-of-the-art access control systems for modern and historic buildings alike. Our engineers use advanced technology to create security setups that are both simple to use, and incredibly effective.
Jump To
- Step 1: Assess Your Access Control Requirements
- Step 2: Secure Your Access Control Credentials
- Step 3: Get Your Access Control System in the Cloud
- Step 4: Integrate Your Access Control With Other Security Systems
- Step 5: Staying Secure
- Is it Time to Upgrade Your Access Control?
Upgrading your access control doesn’t need to be complex or overly costly. In this blog, we outline the 5 steps involved in the upgrade process. Our aim is to make your physical access control as secure and easy to manage as possible. It may even save you money in the long run. You’ll also learn more about integrating with the latest technology available, unlocking a range of useful features to help better manage your building.
.webp?width=960&height=480&name=SALTO%20Access%20Control%20Mobile%20Credentials%20(1).webp)
Step 1: Assess Your Access Control Requirements
When you upgrade your access control, the first thing to do is assess your current solution. Where there might be weaknesses or areas for improvement?
Being proactive is vital to ensure the safety of your site and its occupants. Don’t wait for a security event or break-in before you start to think about upgrading your older systems. The most effective security strategies are the ones that counter threats as they emerge, rather than react to them after the fact.
To do this, you need to make sure you have the best tech available. That doesn’t just mean replacing all the controllers and wiring in your system.
While some of these parts may need to be replaced, most legacy systems are compatible with the latest innovations. This makes the upgrade process much easier and less costly than you may think.
If you aren't sure what upgrades you need, start by asking these questions:
- What areas/points in my site need access control?
- How many people use these areas/points?
- At what times of the day do people need to gain access?
- How many separate access levels are needed?
- How will these upgrades fit into our current system?
- How secure is my current credential technology?
- Can I manage my system remotely?
- Can I initiate a lockdown procedure to prevent access both in/out?
- Do I have a problem with tailgating?
- Are cards and fobs being effectively managed?
To help you better understand your requirements and the options available, you can discuss with one of our security experts at Chris Lewis. We can also advise you on the integrations available to you, to make your security systems easier and more cost-effective to manage.
You should also consider a security audit to find weaknesses and what can be done to improve. The aim is making sure your premises are secure from all security threats and stay protected all year round.
Step 2: Secure Your Access Control Credentials
The main reason building managers look to upgrade their access control is to improve how the security of their credentials, while also making them easier to manage. Introducing advanced credentials is a great way to make your access control more secure. The purpose of these systems is to make sure that only authorised persons can enter certain rooms, buildings, or areas of a site.
Although outdated, key cards and key fobs are still used as a primary security credential for many commercial and residential sites. They are also common in other facilities that need to manage the access of occupants and visitors, like schools, colleges and university campuses.
However, keycards can be lost, stolen, or cloned. This may leave you at risk as unauthorised people can enter your building, maybe even to steal or damage property.
However, as technology advances and becomes less expensive, we’re seeing more buildings install contactless solutions. These can be biometrics and mobile devices, as well as encrypted smart card readers.
As discussed in our access control trends article, biometric credentials have become more and more popular. This is especially true in buildings and sites that need the most secure levels of access control. Such tech is still seen as complex and futuristic but its use is becoming more common in other settings. Facial recognition is especially popular. However, as the tech gets more affordable we’re also seeing iris scanning, contactless fingerprinting, and even voice pattern recognition used to improve site security.
Find out more in our blog on the Benefits and Uses of Biometric Access Control.
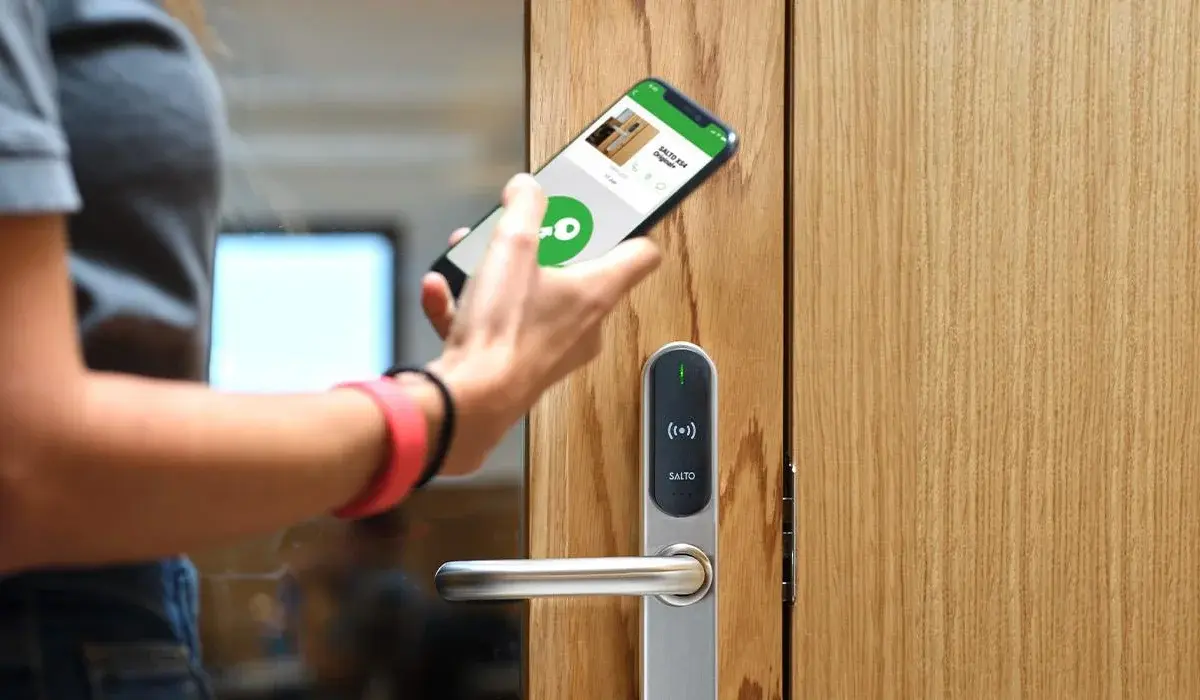
Mobile credentials are an even more useful form of authentication. By downloading a secure app on a pre-approved smartphone, site users can gain entry with no need to even remove the device from their pocket. The reader can recognise their credentials, even at a distance.
Smartphones can also improve the security of your access control another way. They introduce two-factor authentication. This upgrade can be used to enhance your legacy system. After using an access card, fob etc. the system will ask you to enter a PIN on your phone to confirm your identity before it gives you access. This adds another layer of security. So, even if someone gets their hands on a lost keycard, they’ll still be locked out.
.webp?width=960&height=440&name=Access%20Control%20(3).webp)
Step 3: Get Your Access Control Systems in the Cloud
Cloud technology has transformed the way we think about storing and processing data. This, in turn, has had a huge impact on security solutions. This includes CCTV, intruder alarms, and, of course, access control.
The cloud keeps your access control solution safe and easy to manage by storing data remotely on a heavily encrypted server. How does this differ from non-cloud solutions? In the past, access control systems used local servers on site to store the security credentials and clearance levels of everyone with access to the building.
Buying and installing local servers is expensive to begin with. Then you have to think about future updates and ongoing maintenance. All of these will need a technician and IT callouts. There is also a chance that your servers may be damaged or vandalised which can severely impact your access control system.
With no need for physical servers, installing a cloud-based system is quicker, simpler and allows for fast integration with your existing tech. Using plug-and-play controllers, all you need is an internet connection with no need to reconfigure complex firewalls and VPNs. Cloud solutions are also subscription-based, making the cost of your system easier to forecast.
Finally, the cloud also offers easy scalability. This is vital if you're a growing business and need to add extra control points to your system. This is even possible if they are in different buildings or on separate sites.

Step 4: Integrate Your Access Control With Other Security Systems
Upgrading the components within your access control system is just the start. There are more ways than ever to integrate access control technology with other systems to increase your building or site security.
For example, you can pair IP cameras with access points. When someone attempts entry, cameras will record them. In the event of a security breach, this allows security operators to look for the footage to see who unlocked the door.
CCTV integration can also help detect tailgating, something not possible with outdated systems. To learn more, read our article “CCTV & Access Control: Everything You Need to Know.”
Think about what else you can integrate. Pair your access control with lift controls to make sure staff and visitors can only stop at certain floors. Or, integrate it with your security alarm to trigger when individuals who have been flagged try to enter.
There are even more practical applications that go beyond increasing security. Offices and workspaces are evolving thanks to the rapid adoption of smart building systems. These allow you to manage lights, sound systems and even your heating or cooling.
For example, your access control can tell smart building to switch on all the lights when the first person enters in the morning. Access control software can also link up to third party applications and software such as G Suite, Slack, and Office365 to help with administrative tasks.
.webp?width=960&height=440&name=Access%20Control%20Verkada%20(1).webp)
Step 5: Staying Secure
Having the most secure technology and systems installed is only part of the equation. Making sure your building staff know how to operate and manage your access control is vital. You should aim to run audits on a regular basis. Keep an up-to-date record of how many credentials have been issued, whether they've expired, and the entry privileges of each person to reduce the risk of a security breach.
You should also test the components in your system the same way you would alarms or fire safety systems.
Is it Time to Upgrade Your Access Control?
Even if your access control system is only a few years old, you should still check regularly to see what new tech is available and how it can improve your security.
Not only is this crucial to keep your building secure, it also gives you integration opportunities that can be useful for managing a commercial premises or facility. Upgrading your access control doesn’t have to be expensive or complex either, with various solutions available to meet any requirements.
If you're interested in an access control system that will keep you on the front foot against any security threat for years to come, we're here to help. With over 30 years' experience creating top-of-the-line security systems, our expert engineers can create a solution that is completely bespoke to your needs. Simply fill in the form below, and we will be in touch.
Talk to us about your CCTV and Access Control requirements
Complete the contact form below and we will get back to you very shortly.

Luke Lewis-Rippington
Related Posts
OSDP vs. Wiegand: Why Your Access Control System is Stuck in the 1980s
Alright, let’s talk access control—the tech that determines whether you walk through the door like a VIP or get stopped like an imposter in a bad heist movie.
4 Access Control Trends for 2025
Access control has come a long way from receptionists and sign-in sheets. New access control technology, bolstered by Internet of Things (IoT) technology, is bringing higher levels of security than.
CCTV & Access Control: Everything You Need to Know
Technology is constantly advancing, and businesses constantly have to rethink their security strategies to counter the latest changes. This is especially true when it comes to CCTV and access.