When considering which CCTV cameras and systems to install, security is paramount.
We’re not just talking about the ways in which CCTV can help secure your business or property. Primarily, cameras are a deterrent to potential intruders, monitoring activity, and intelligently integrating with other security systems. However, we also need to think about how well protected they are in terms of cyber security. It’s an unfortunate inevitability that hackers and malicious actors will try and gain unauthorised access to your CCTV system.
This doesn’t just apply to CCTV - in fact, any device connected to a network is vulnerable to attack.
Jump To
- How Can Hackers Access Your Camera?
- What Are the Threats of Cybercrime?
- How Can I Prevent Cyber Attacks?
- Prepare for a Connected Future
We’re continuing to see a wide adoption of IoT (internet of things) devices everywhere, ranging from household appliances such as fridge freezers, to intelligent industrial machinery. In 2021, the number of connected devices is set to hit a staggering 46 billion according to Juniper Research. This number is expected to grow exponentially over the next decade with an estimated 125 billion IoT devices being connected by 2030.
On one hand, this can help improve our day-to-day lives through convenient automation. However, this presents hackers with even more ways to invade our privacy.
This blog explores CCTV and cyber security in more depth. We’ll show how hackers can gain access to CCTV systems, the risks and consequences of hacking attempts, and ways to help protect your home or business from cyber security threats.
.webp?width=960&height=440&name=Cybersecurity%20(1).webp)
How Can Hackers Access Your CCTV Cameras?
Those who want to learn how to hack CCTV and other IoT devices have more ways of doing so than ever, with information and resources easily available online. It’s true that some hackers exploit systems with good intentions, revealing security flaws to companies who are then able to update and improve their systems. However, there are those who hack systems to gain information on individuals and companies, usually for their own personal gain.
An overwhelming majority of hacks are carried out remotely. While local hacking does still occur, these are easier to trace and require more time and effort to perform. In contrast, remote hacks can be done anywhere, at any time, even from a remote location hundreds of miles away. All hackers need is a reliable internet connection and a way of sourcing your security credentials.
Even the newest, most expensive CCTV cameras are prone to such hacks. IP cameras are a popular choice thanks to their quick setup, reliability, and feature set. These cameras capture video and then transmit that data over the internet, via WiFi. IP cameras have an associated IP address which hackers are able to easily locate. However, the hard part is gaining access to these cameras. Hackers need to successfully guess the admin username and password associated with a camera. If successful, hackers will be able to view video footage and maybe even change the settings of your camera, potentially leaving you exposed to intruders. This is exactly what happened in 2017 when hundreds of Hikvision cameras and DVRs were hacked using the manufacturer’s default setup password.
Another way hackers can access your cameras is through backdoor exploits. While manufacturers are proactive in combating threats, sometimes they can unintentionally leave a “backdoor” for hackers to enter their systems, retrieving and leaking the personal information of customers. These credentials can allow hackers to access CCTV systems, obtaining video data, manipulating DVRs, and locking users out by changing their account details.
This can cause a huge amount of disruption to businesses while also leaving valuables potentially exposed to criminals. If you are a business owner who hasn’t taken measures to improve the defence of your CCTV system against cyber threats, you are putting your employees, customers, and assets at risk.
.webp?width=960&height=440&name=Cybersecurity%20Lock%20(1).webp)
What Are the Threats of Cyber Crime?
Let’s look at the harm that can be caused by malicious actors who manage to hack CCTV camera systems. The most common example we think of is someone having access to live video of our homes or workplaces, as well as any archived footage that may have been stored recently. Such invasions of privacy are not only harmful to our wellbeing but can leave us exposed to other threats.
In one scenario, a hacker may be able to relay footage of your home or business premises to criminals along with your address. They will have information on the layout of your home or commercial address, where you keep valuable assets, and whether the property is vacant.
It may sound like something plucked from the pages of a spy thriller though footage can also be used to threaten or blackmail you. There is also a possibility hackers can access the microphone feature of some cameras to make unauthorised communication with anyone inside a property. This can be particularly concerning if minors are present at the address.
Earlier this year, hackers were able to gain access to more than 150,00 Verkada cameras around the world, including those installed in homes, factories, healthcare facilities, and even prisons. Even larger companies such as Tesla and Cloudflare were victims of this attack, proving just how vulnerable CCTV can be, regardless of industry and security budget.
If you have a fully integrated smart home or smart building then there is a chance hackers can gain access to other devices as well as data and credentials. Cyber security threats can be scary though there are steps that can be taken to prevent the harm they cause and mitigate their harmful effects.

How Can I Prevent Cyber Attacks?
One solution that can help tackle cyber security is to implement a system of cameras connected to a local server. This is how traditional CCTV systems have worked in the past with cameras connected to a DVR where footage can then be accessed and reviewed.
While this can prevent hackers from gaining unauthorised access remotely, it leaves you open to physical attacks on your CCTV system. Intruders who gain access to a control room will be able to tamper or destroy footage, or even steal your storage hardware. Local storage may be considered a safer option to some, but it severely limits the features and functionality of your CCTV.
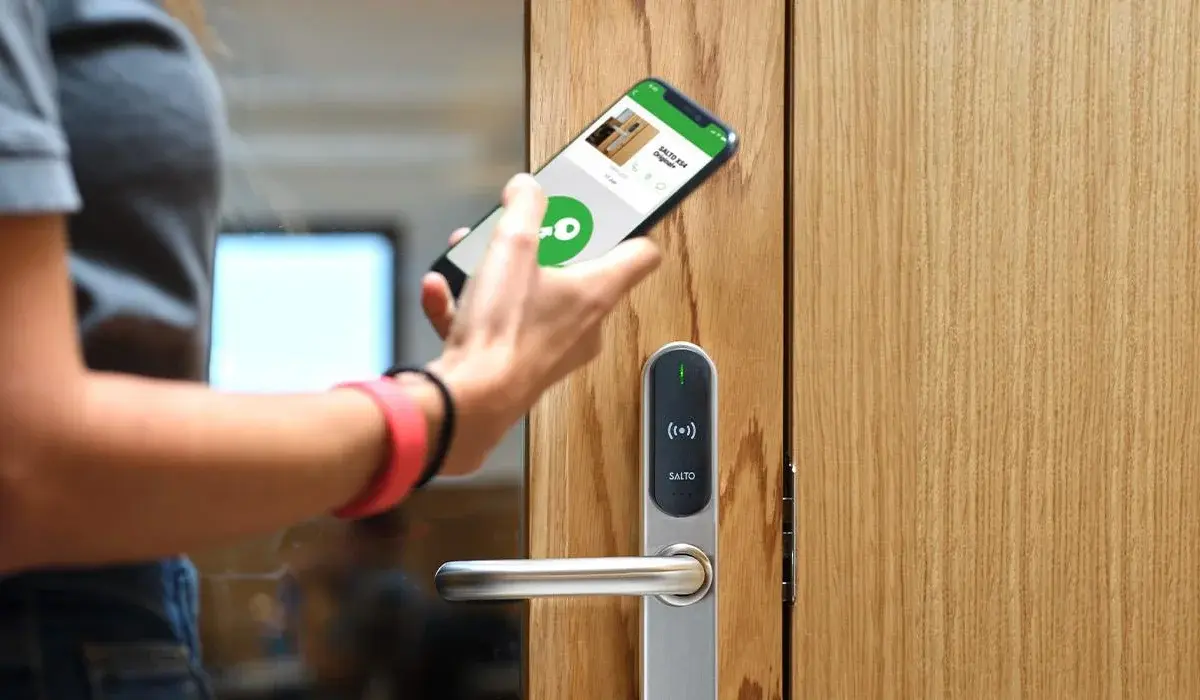
For example, you won’t be able to monitor live camera feeds or any recorded footage remotely. In contrast, connected CCTV systems allow authorised users to monitor video in real-time anytime, anywhere using a connected device such as a smartphone or tablet. Meanwhile, traditional setups only allow viewing via a screen directly wired to the CCTV system.
You also lose the ability to enable push notifications. One proactive feature offered by cameras connected to the internet is the way they flag events via audio recorders and motion sensors. Again, security operators won’t be able to stay notified of these events remotely which reduces their ability to actively respond to threats.
Finally, you also lose access to the power and convenience of cloud CCTV storage. Both new and existing CCTV systems can be upgraded to allow cloud storage, keeping any recorded footage on a remote server where it can be accessed by authorised users. This reduces the need for expensive proprietary hardware and technician callouts, too.

Cameras connected to the internet may be vulnerable though there are measures you can take to improve your defences against cyber security threats.
Learning more about the methods hackers use to access cameras can help you better combat them. Once cameras have been installed, operators can fall into the common trap of failing to change the admin username or password. Therefore, hackers have been able to commandeer cameras by using the default security credentials provided by manufacturers. This could be a simple word or series of numbers.
Even if your CCTV system boasts the most versatile cameras, firewalls, and network protocols, this method can easily bypass these barriers. Make sure you change the username and password - the strongest passwords are usually those that consist of three words, or a combination of upper/lower case letters with numbers and special characters.
When installing CCTV cameras, our security experts at Chris Lewis Group will advise you on how to keep your cameras as secure as possible. Firstly we change all the usernames and passwords from default. If the system supports it then we also set up two-factor authentication (2FA). We try to make sure all the cameras are on their own dedicated network and not accessible by other workstations on the LAN.
.webp?width=960&height=440&name=Verkada%20Cloud%20CCTV%20Dome%20Cameras%20(1).webp) In their battle against hackers, CCTV manufacturers will attempt to strengthen the integrity of their products by releasing regular firmware updates. These are designed to prevent malicious actors from obtaining user credentials.
In their battle against hackers, CCTV manufacturers will attempt to strengthen the integrity of their products by releasing regular firmware updates. These are designed to prevent malicious actors from obtaining user credentials.
When choosing a CCTV system, make sure you research brands thoroughly and that their cameras offer the best level encryption. Again, our security experts at Chris Lewis can advise you on the best solution, giving you peace of mind.
Manufacturers are proactive in their fight against cyber security threats and making sure customers are as protected from hackers as possible. They constantly work to review their security solutions, helping to prevent “backdoor” access. They will deploy regular firmware updates for cameras that need to be installed to make sure your CCTV is secure against the latest vulnerabilities.
Our ongoing support and maintenance packages will ensure your CCTV cameras are always performing at their most secure.
Prepare for a Connected Future
The hard truth is that we can’t avoid the rapid adoption of smart, interconnected technologies. There’s a good chance that, sitting here reading this blog, you are already surrounded by connected devices, with a smartphone in your pocket and maybe even a smartwatch on your wrist.
The convenience this technology brings into our lives is too valuable to ignore, even if there are glaring security issues.
This applies to CCTV and how many cameras there are now compared to how many there will be in the future. The affordability of cameras and the convenience/scalability offered thanks to cloud storage means that we’ll see even more cameras installed.
Ultimately, it’s a question of balancing security risks with the freedom and power offered by connected technologies. However, there are steps manufacturers and CCTV systems operators can take to fortify their defences against cyber security threats. As we’ve already discussed, awareness is key.
While manufacturers continue to be vigilant in upgrading their cameras, their systems, and the software that powers them, we need to be maintaining our CCTV regularly, upgrading to the latest firmware and making sure our credentials are secure and updated to prevent unauthorised access.
To reap the benefits of intelligent CCTV systems we also need to take on board the risks. However, as we’ve discussed, these can be mitigated by improving your knowledge of how these systems work while working with professional installers. In a future where technology will be dominated by smart homes and IoT, being equipped for this new digital landscape is essential.
Talk to us about securing your CCTV
Complete the contact form below and we will get back to you very shortly.

Luke Lewis-Rippington
Related Posts
4 Access Control Trends for 2025
Access control has come a long way from receptionists and sign-in sheets. New access control technology, bolstered by Internet of Things (IoT) technology, is bringing higher levels of security than.
CCTV & Access Control: Everything You Need to Know
Technology is constantly advancing, and businesses constantly have to rethink their security strategies to counter the latest changes. This is especially true when it comes to CCTV and access.
Why You Need to Upgrade Your CCTV Cameras
The risks of using old CCTV cameras are no secret. A slow, outdated legacy system can increase the chance of crime on your property and open up your business to serious threats and liability.