Access control has come a long way since the days of keypads and card readers. Now, businesses across the globe are being accessed with a wide range of different credentials - from mobile phones, to fingerprints and facial recognition.
But one thing has remained the same. For as long as businesses have used access control, they’ve needed a simple way to control and manage access, and add new user credentials to their database.
Jump To
- What Is Cloud Based Access Control?
- How Does Cloud Based Access Control Work?
- Managing User Interfaces & Permissions for Cloud Access Control
- Traditional Access Control vs Cloud Based Access Control
- Can I Integrate Access Control With My Other Security Systems?
- Is Cloud Based Access Control Expensive?
- The Best Cloud Based Access Control Systems
- Ready to Get in the Cloud
Sure, you might think your Excel spreadsheet and key card printer work a treat... but the reality is that these traditional legacy systems are clunky and expensive to maintain. Not to mention the freedom for cloning, misplacement and theft.
That's why, If you’re looking for complete control over your access control system in 2024, it’s definitely worth getting into the cloud. Cloud-based access control solves a lot of the modern challenges linked with access. These systems give businesses the flexibility to manage from one single, centralised system.
Our latest blog explores what cloud-based door access control is and the best systems available on the market. We’ll dive into the benefits of switching to the cloud and the thoughts needed to modernise how you gain access.

What Is Cloud Based Access Control?
Cloud-based access control systems work by enabling the user to manage all doors, gates and access points from a single, centralised system on an internet-connected device. Admins can monitor and edit access information anywhere, at any time - whether on-site or on-the-go.
Cloud-based access control simplifies physical security, integrating multiple systems into a slick, intuitive and user-friendly interface. It makes it a great deal easier to add and remove users, access auditing reports, edit door schedules and assign permissions, all from a single software and device. With a number of key benefits:- Simple Management with Full Remote Control
- Instant Access Alerts & Warnings
- On-the-Go Permission Editing
- Exportable Access Logs
- Entry Event Timelines
- Live Occupancy Monitoring
- Remote One-Touch Visitor Access Granting
The user interface is the brains behind your entire access control system. It reduces the need for spreadsheets and paper sign-in sheets. It gives admins the tools to issue or edit credentials to people quickly and efficiently. Whether that be through key fob, biometric access or mobile phone credentials. This makes the process of distributing access far more reliable and trustworthy.
These systems usually come with centralised management, real-time updates and performance diagnostics to ensure the technology is constantly improving, patching faults and addressing cybersecurity threats far quicker than an older system.
Not only does this add extra peace of mind for the operator, these systems are also extremely convenient for both admins and end-users. Most cloud-based platforms are quick to deploy and easy to learn without any extensive training or expert know-how.
How Does Cloud Based Access Control Work?
Unlike legacy access control, a cloud-based solution works by storing data in the cloud, rather than an on-site server. This means users get constant access to their data, making changes to user permissions from any device.
The system moves the server from the premises to a data centre, which hosts the equipment entirely off-site. But, of course, the door readers and key fob pads need to remain at the on-site entrance points to allow access to members of staff and chosen users.
Like traditional access control, a cloud-based system requires a connection between your hardware and a central server. Think: doors, locks, card readers and keypads. All your access control hardware is connected to the internet, using a wired or wireless connection; putting your updates and system changes into rapid action.
Managing User Interfaces & Permissions for Cloud Access Control
So who is responsible for managing the interface? Well, it’s really up to you. For security purposes, all cloud-based access control solutions require ID verification before admin permissions are given. This is usually a pin code or username and password.
Though, you’ll be able to simply add admin permissions for nominated people in your company, letting you choose who can make changes and add/remove users. This is especially useful for large HR teams tasked with monitoring building occupancy and staff arrival times.
Once logged in, the interface puts all your credentials, information and access activity right at your fingertips. Even if you have thousands of employees and unique permissions for each.
Traditional Access Control vs Cloud Based Access Control
Traditional access control systems need a database to be placed on-site using expensive server hardware. This typically demands a lot of physical space, regular updates and costly repairs.
Cloud hosted solutions are the answer to this problem. They give the user a lower initial capital outlay, saving money on server hardware maintenance. Not to mention, reducing the risk of the physical weaknesses linked with on-site hardware.
And, without the need for physical on-site servers, the installation process becomes far quicker and simpler. There’s no need to poke holes in firewalls or setup complex VPNs. It’s simply a case of using plug-and-play controllers and a windows connected device to edit permissions and monitor events.
Unlike on-premise access control, cloud-based systems can also undergo routine software updates and regular firmware patching remotely. As such, the system offers automatic updates when a newer version is released. This makes sure that your technology is protected against any emerging threats.
Can I Integrate Access Control With My Other Security?
Cloud access control is endlessly scalable. It can integrate with your other security systems via open application programming interfaces (open APIs). For example, the cloud can integrate with payroll to improve the accuracy of your timesheets. Integrate with G Suite, Okta and Office 365 to add and remove access control credentials as people come and go from your team.
You'll even be able to link your smart CCTV to enable face verification. This feature instantly verifies each credential using face ID. It allows you to map events to relevant CCTV footage and even detect when people have tailgated through the door.
Is Cloud Based Access Control Expensive?
One of the biggest misconceptions about cloud-based access control is that it’s more expensive. Sure, certain packages will have a hefty upfront price tag attached to them, but in a lot of cases, they actually make for a more than sensible investment.
Most of the time, new cloud-based access control owners will be upgrading from an existing legacy system. This means they’ll be able to keep their existing control readers, access cards, locks and power supplies - saving more on expensive hardware, which makes up a large part of the expense. In this scenario, it’s quite literally a case of changing the door controller. No hardware installation fees. No wasted time.
A variety of leading access control brands even offer subscription payment plans, rather than an upfront fee. Business owners can choose from a sample of packages that fit their needs and budgets. Instead of spending money on technology they’ll never need or use.

The Best Cloud Based Access Control Systems
There are a wide variety of high-spec cloud-based physical access control systems available on the market, with a range of features and perks to suit your business. At Chris Lewis Group, we understand that this makes it even more challenging to find the right system for your needs.
Switching to cloud may seem daunting, but we’ve got you covered. Read on to discover three of the most effective cloud-based access control systems available today. We’ll explore the key features and what each can offer your business.
Verkada

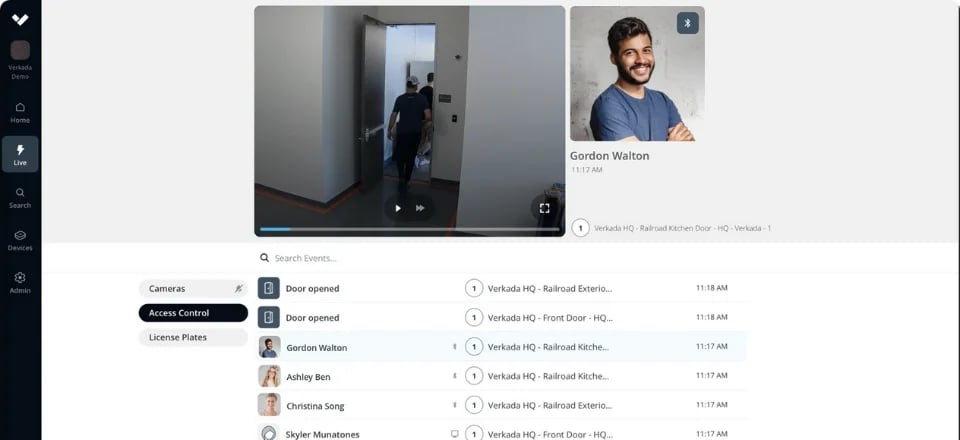
Verkada is one of the biggest names in cloud based access control. The company’s technology combines enterprise-grade hardware with a cloud-based management interface that’s simple, secure and easily scalable.
Whether upgrading or starting afresh, it’s incredibly easy and efficient to get started with Verkada access. Starting with their plug-and-play ‘Access Controllers’, users are able to instantly connect their existing door readers to the system. This setup makes it simple to add new doors and entry points as your company grows.
Verkada is especially great for businesses looking for complete video surveillance integration and visual confirmation. Using their cutting-edge video processing technology, admins are able to get 24/7 visual access to their entry points from a mobile device. This allows them to respond to access alerts safely and proactively.
The Rundown
- Easy visitor management across all sites and users
- Verkada Pass App for touchless access - Available on IOS & Android
- Integration with Verkada systems such as video surveillance
- Anti-Tailgating Detection using video
- Unlimited hardware and user additions
- Automatic firmware updates
- Secure remote access on any device
- 10-year warranty on all hardware
Avigilon Alta

Avigilon Alta (formerly Openpath and Ava) offers an industry-leading keyless access control solution. Their systems allow admins to create a safer, more secure space with complete access control, built for scale across multiple locations with thousands of users. Avigilon Alta centralizes security management with robust cloud-based software and seamless integrations, all managed from a single pane of glass.
Through integration, you’ll be able to gain clear insights about your operation and security that’ll help to make more informed decisions about upgrading. Avigilon Alta gives you unmatched visibility and control over all your locations, so you can more with less investment including updating software automatically, automate processes and scale as your business needs.
The Rundown
- Lower costs with automatic system-wide updates
- Automate processes across your enterprise
- Adaptable technology scales up or down with ease
- Increase awareness with business intelligence tools that ingest data from Avigilon Alta’s open API
- Maintain audit logs of admin portal activity and control who has access to your data
SALTO KS

Salto is one of the biggest names in the access control industry. Specialising in high quality lock and tagging hardware, they’ve been a popular choice for businesses looking to shore up their security with key cards and fobs.
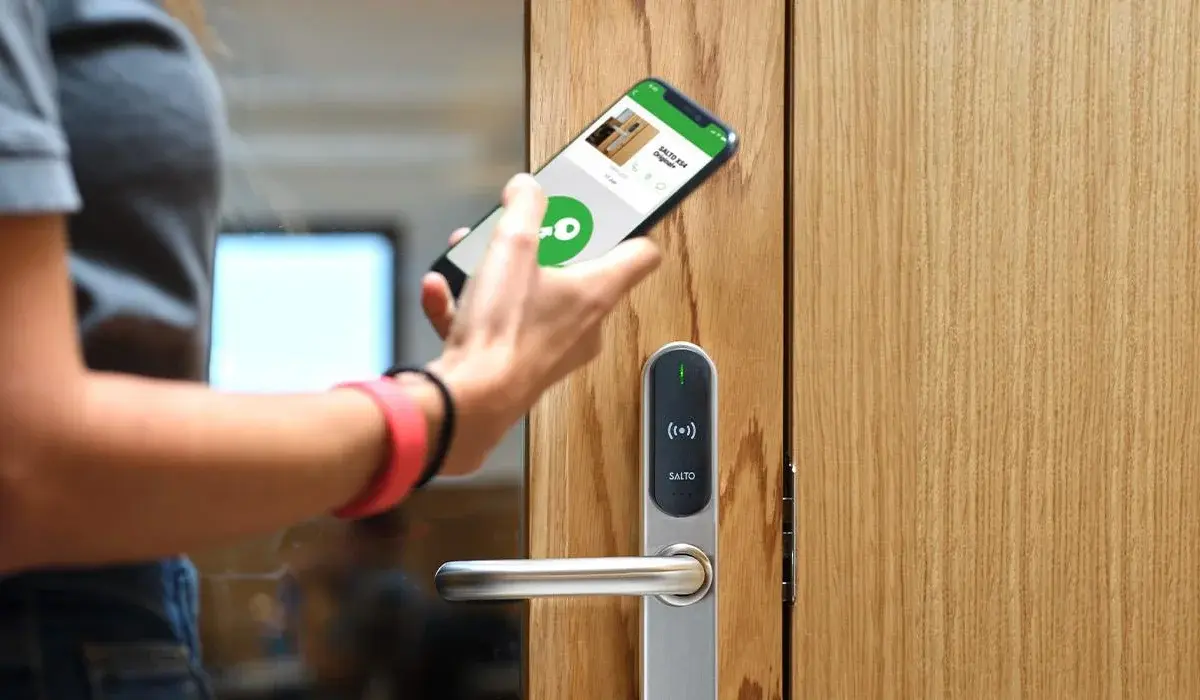
Their cloud-based access control system is no different. Salto KS uses a slick and flexible interface that is built around your business’ needs. With an easy-to-use mobile app, admins can assign permissions and roles to their users and track entry events from all over the world. Not to mention, staff are able to open doors using their smartphones and send digital keys to guests.
SALTO KS access control makes for an especially great choice is you’re looking for a system that grows alongside your business. Backed by some of the most innovative minds in the field, SALTO KS uses remote maintenance to constantly update the system, increasing security and efficiency.
The Rundown
- Range of door control hardware: smart locks, wall readers, tags, mobile access and key cards
- Powerful entry data insight
- Centralised app and web-based control management
- Real-time firmware and system updates
- Mobile credential issuing & management
- Global scalability
Ready to Get in the Cloud?
If you’re concerned over the sureness of your access control technology, now is the time to upgrade. Leaving it late could cause troublesome security issues for your business, staff and assets.
At Chris Lewis Fire & Security, we understand the importance, reassurance and convenience a reliable access control system can have for your business. Our installation experts are highly experienced in the spec, design, installation and aftercare of cloud-based access control technology.
We primarily work with the industry’s leading manufacturers to design bespoke security solutions that benefit both your building and the people inside.
Speak with one of our experts today to see what we can do for you:
Submit the form below and we will get back to you very shortly.

Luke Lewis-Rippington
Related Posts
OSDP vs. Wiegand: Why Your Access Control System is Stuck in the 1980s
Alright, let’s talk access control—the tech that determines whether you walk through the door like a VIP or get stopped like an imposter in a bad heist movie.
4 Access Control Trends for 2025
Access control has come a long way from receptionists and sign-in sheets. New access control technology, bolstered by Internet of Things (IoT) technology, is bringing higher levels of security than.
CCTV & Access Control: Everything You Need to Know
Technology is constantly advancing, and businesses constantly have to rethink their security strategies to counter the latest changes. This is especially true when it comes to CCTV and access.