Access control has come a long way from receptionists and sign-in sheets. New access control technology, bolstered by Internet of Things (IoT) technology, is bringing higher levels of security than ever before. As we head into 2025 and beyond, this sector will only continue to evolve.
Predictions for the Top 4 Access Control Trends
- 1. Mobile Credentials for Access Control
- 2. Biometric Access Control Credentials
- 3. Cloud Based Access Control Systems
- 4. AI and Machine Learning in Access Control
- What's Next for Access Control?
As a business it’s important to be aware of such high-tech access control technology trends to ensure the safety of your employees and the security of your premises.
We’re The Chris Lewis Group, a bespoke fire and security system installer based in the South of England. We’ve designed and installed state-of-the-art security measures in buildings ranging from historic libraries to cutting-edge research sites.
Today, we'll explore four key access control trends for 2025, explaining how each of them works, and how they can make a positive change to managing access.

1. Mobile Credentials for Access Control
Keyless technology is fast becoming the future of access control. This is thanks to the advent of smartphones. According to SJA, the mobile access control credentials market is set to reach over $750 million in revenue by 2028, up from only $295 million in 2022.
We’re seeing more businesses move away from traditional access control options, like key cards and fobs. If you're buying a new physical access control system, you should make sure it either supports mobile devices now, or in the future.
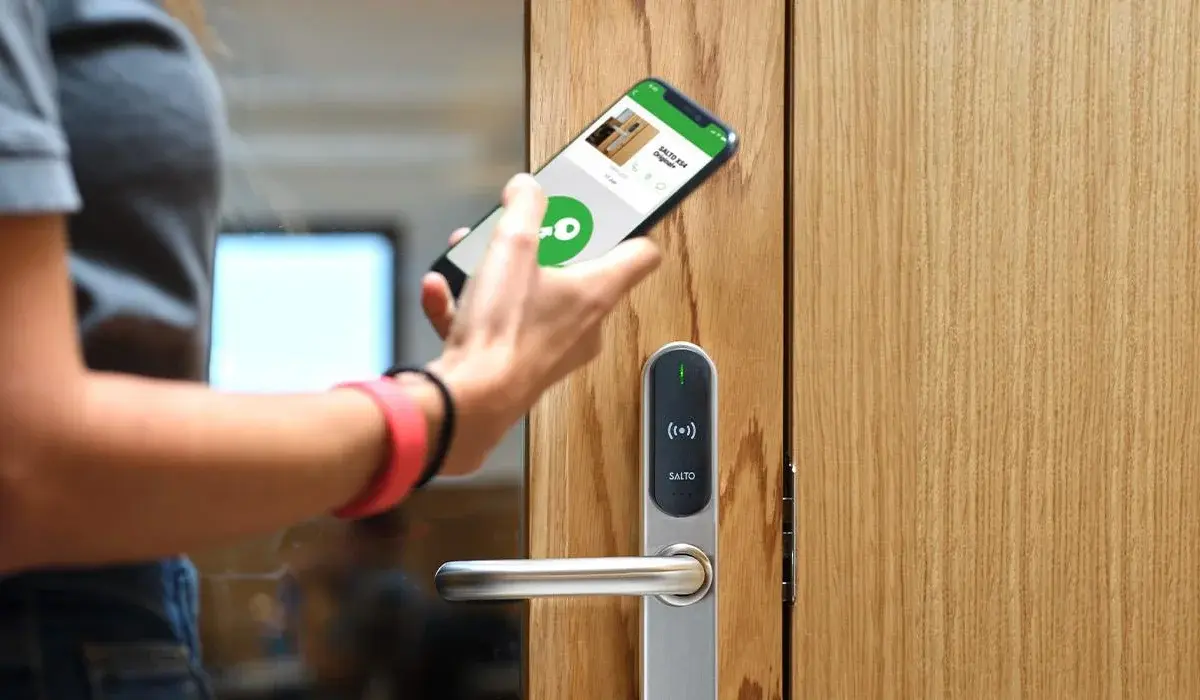
How does contactless mobile access control work? Instead of a key card or key fob, which is costly, slower to set up, and easily lost, users download security credentials directly to their smartphone.
The access control operator can send them a link to click, or an app to download, which will give them their credential. This means you can issue access credentials to a new hire or contractor in seconds.
A mobile-capable reader will check these credentials using a Bluetooth, Wi-Fi, mobile, or NFC connection. To gain access, you simply take your phone and wave it in front of a reader. In some cases you can even wave a hand, and the reader will detect the phone credentials in your pocket. Like with a traditional access card or fob, the system then denies or grants access. It’s that easy.
No one likes catching the office cold or flu, and with contactless mobile access control like this, businesses and schools now have a more sanitary, hands-free method of gaining access.
Smartphone access control systems can also be used in tandem with multimodal or multi factor authentication (MFA) as an extra layer of security. This is common in industries like oil, gas, data centres and power plants. Along with your smartphone, you will use a PIN, or biometric data like a fingerprint or facial scan.
2. Biometric Access Control Credentials
Biometric credentials can go a step further, and remove the need for physical credentials (even smartphones) completely. Biometric credentials include fingerprints, voice patterns, iris scanning, facial recognition and even DNA. Using biometric credentials isn’t just convenient but highly secure as it's quite difficult (and very illegal) for someone to steal your finger or your eye.
The use of identity authentication technology has risen rapidly in recent years. In a report published by market research company Technavio, the Biometric Access Control Systems Market Size is predicted to grow by $4.38 billion between 2023 and 2028. This is a compound average growth rate of 7.77%.
Facial recognition is getting more common as a means of touchless access control. It’s already a common way of accessing smartphones without needing a passcode or pattern. If your access control and CCTV systems are integrated, it’s also commonly used for visual verification. This technology is a form of multifactor authentication that detects if the person using a credential is who they claim to be. If not, mobile warnings are sent to the security team, flagging unauthorised access.
Although facial recognition technology has been around for a while, integration with security systems has been limited. In the past, it was much too expensive and inaccurate, and there were concerns around privacy. But as face scanning technology improves in quality, and prices fall, it’s become far more common.
Attitudes towards biometric credentials are also shifting. With both 3D face recognition and fingerprint scanning now commonplace in smartphones in 2024, we’re now much less concerned about privacy issues.
It's important to also be aware of other emerging alternatives. These include iris scanning, contactless fingerprints, and even the use of voice patterns.

3. Cloud Based Access Control Systems
Cloud based access control systems are the invisible force behind how access control is being revolutionised.
Cloud computing has completely changed our day-to-day lives. It’s had a huge impact on how we think about storing, managing, and processing data. For example, photos and videos from our smartphones no longer need to be stored on a computer, or portable hard drive. Instead, they can be instantly uploaded to remote servers, and retrieved whenever, wherever.
This shift from local to remote (or "cloud") server storage has had the same impact on access control. It has become a cornerstone for today's business security systems.
In the past, companies would host their data on-site with bulky and expensive hardware. This doesn’t just demand a lot of physical space, but is costly to install, maintain, and upgrade. Switching to a cloud-based solution is more cost-effective, convenient and scalable. It also means admins can remotely manage the system, 24/7, with instant notifications of component failures, security concerns, or event alarms.
With no need for physical servers, installing access control systems is quicker and simpler. If you’re switching from on-site servers, integration with your existing access management system is quick and easy, too. Controllers are plug-and-play, and all you need is internet access. No poking holes in firewalls or setting up complex VPNs. Once it’s set up, security managers can change access privileges easily, and adjust levels of security from any internet-enabled device.
Maintenance is also easier. On-premise storage systems need to be checked by technicians for security risks. Cloud-based systems are more dynamic. Updates are automatically downloaded and installed constantly. This reduces the risk of a sophisticated cyber attack or virus disabling your system. Troubleshooting, security firmware patches, server maintenance, data backups and software updates can also be performed remotely, off-site.
Imagine if the computer that stored the company data for 500 of your staff broke down! You would have to collect all 500 access control cards and re-enrol these cards on a fresh new database. All access control doors would also have to be reprogrammed. Running your systems in the cloud means that there is no single point of failure with this database.
Scalability is another key consideration. On-site security system servers have a connection limit. If you increase your system size or expand to a new site, you’ll need to replace the server with a bigger one - an expensive upgrade. A cloud system can scale from one site to many. If you go over your connection limit, all you need to do is increase your subscription fee.
Cloud access control also integrates with other security solutions via open application programming interfaces (or "open APIs"). For example, cloud door access control systems can integrate with payroll software to help keep accurate timesheets. Or it can integrate with facility management software, and raise a work request automatically if there is a problem with a system component.
You can also use it to establish virtual zones within a building. With these zones, you can monitor which employees have entered what area and at what time of day. By integrating with CCTV cameras, you'll also be able to set up visual identity verification.

4. AI and Machine Learning in Access Control
The latest trends in access control, Artificial Intelligence (AI) and Machine Learning (ML) are revolutionising the field. These systems can analyse vast amounts of data, identifying patterns, predicting potential threats and optimising access policies.
AI can identify unusual behaviour patterns, like multiple unauthorised access attempts or suspicious activity, and flag them to security teams. When paired with CCTV systems for visual verification, AI can improve accuracy. With this technology, people can be correctly identified, even in low light, or with their faces partially covered.
At the moment, this technology is still in its infancy. As AI and ML continue to advance, their integration into access control systems will become even more sophisticated, leading to even greater levels of security and convenience.
What's the Future of Access Control?
If innovations over the past few years are anything to go by, access control will only become more robust in the near future. As we’ve already mentioned, AI is likely to drive the next leg of development. Looking even further ahead we may even see implants and neural network technology revolutionise the way we think about enhanced security credentials, as far-fetched as it may sound now.
If you’re looking to install a system that ensures your site will be securely accessed for years to come, we’re here to help. With over 30 years of experience installing the latest, most advanced security systems available, we can create a solution that works for you. All of our set-ups are completely bespoke to your needs, and we will collaborate with you to ensure your system meets your every requirement.
Interested? Just fill in the form below, and we will be in touch.
Want to learn more about the access control systems we install? Check out our Access Control Installers page, or our Access Control blogs.
Talk to us about your Access Control requirements
Submit the form below and we will be in touch shortly.

Luke Lewis-Rippington
Related Posts
OSDP vs. Wiegand: Why Your Access Control System is Stuck in the 1980s
Alright, let’s talk access control—the tech that determines whether you walk through the door like a VIP or get stopped like an imposter in a bad heist movie.
CCTV & Access Control: Everything You Need to Know
Technology is constantly advancing, and businesses constantly have to rethink their security strategies to counter the latest changes. This is especially true when it comes to CCTV and access.
Why You Need to Upgrade Your CCTV Cameras
The risks of using old CCTV cameras are no secret. A slow, outdated legacy system can increase the chance of crime on your property and open up your business to serious threats and liability.